Way back in 2017, the CA/Browser Forum voted on Ballot 193 – 825-day Certificate Lifetimes, which passed. In short, this means that CA issued certificates issued after March 1st 2018 can not have a validity period longer than 825 days. macOS Catalina implements this change, as described in Requirements for trusted certificates in iOS 13 and macOS 10.15. So it’s been a long time coming, but most of us are just now realizing how this affects us.
This also applies to Self-signed certificates, like the ones issued for VMware vSphere and related solutions, like NSX-T and others, where the default age is 10 years or so.
Chrome on macOS is a bit more strict than Safari and Firefox, and doesn’t display an obvious way of proceeding if the certificate expiry date is more than 825 days from the time it was issued:
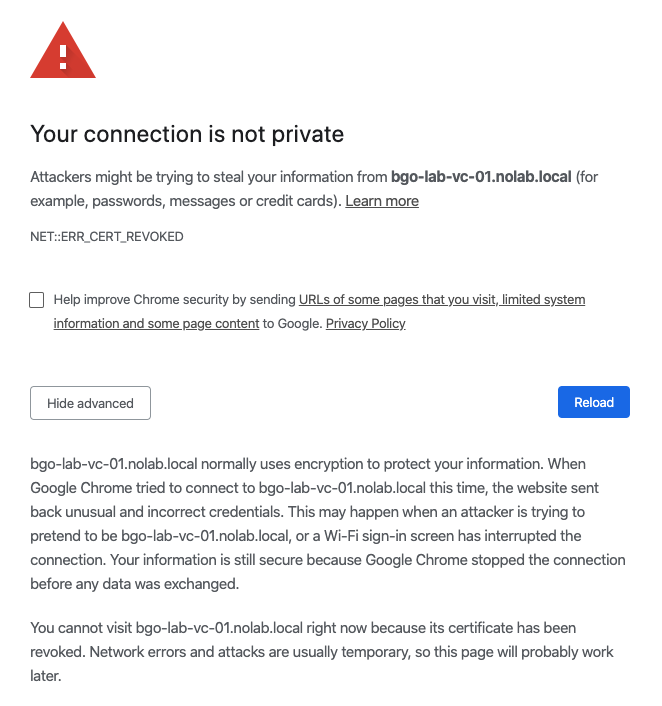
As shown above, there is no “continue at your own risk” option here. There are, however, a couple of ways to work around this.
Method 1#
Cheat! Chrome has a “hidden” option to bypass certificate issues. Simply type thisisunsafe into the browser window, and it will magically let you continue to the site! Granted, this isn’t a permanent solution in any way, but it might help you out of a pickle.
Method 2#
The second method is more permanent that Method 1, but also not advisable unless this is in a lab environment.
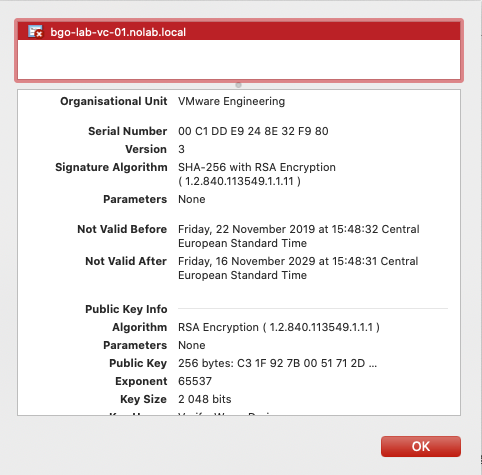
Import the certificate into your macOS keychain. Open the certificate in Chrome, and simply drag the certificate icon to your desktop (or somewhere else)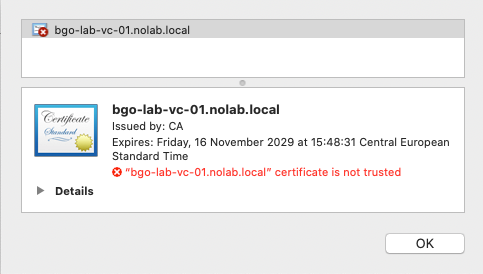
Find the exported certificate, and double-click on it to import it into your keychain. It should then appear under Category -> Certificates.
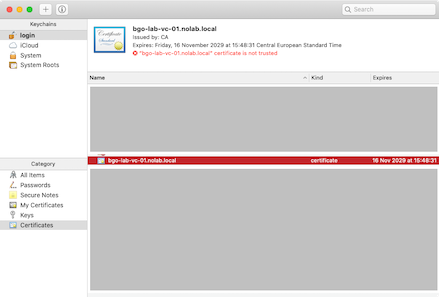
Reload Chrome, and you should be able to open the site without issues.
Method 3#
Start Chrome with flags. Chrome also has a few command line flags, or arguments, and one of them is -ignore-certificate-errors. Guess what that does?
I have created an alias on my MacBook that looks like this: chrome-cert='open -a "Google Chrome" --args -ignore-certificate-errors'
So if I need to turn off certificate error warnings for a period of time, all I have to do is quit Chrome, if it is already running, and start it in terminal with the chrome-cert command.
Obviously the best way to permanently fix this is to use proper CA issued certificates (I guess that’s Method 4, really), but at least there are workarounds that allows the continued usage of Chrome to manage your systems if replacing the certificates is not an option.
I’m sure VMware, and others, will implement the max age of 825 days going forward but that is going to take some time — But in fairness, the decision to not support >825 day certificates was taken back in 2017 so it should really have been taken care of already.
